Today, I am very excited to report that we will be taking a look at one of my favorite torrent sites. Allow me to introduce you to 1337x.
History of 1337x
When one torrent site crumbles, another one rises up in its stead. And, as you may already be well aware, torrent sites are very prone to crumbling. Constantly being hunted by various entities, torrent sites are some of the most volatile on the web. Sites are constantly in flux. Either moving domains, jumping to different countries, being shut down, or being launched. It is a constantly changing enterprise.
Although it was originally founded in 2007, this torrent site did not begin seeing a spike in popularity until 2016, coinciding with the shutdown of the extremely popular torrent site, Kick Ass Torrents. Along with its newfound popularity, 1337x hit the scene with a total site redesign, presenting itself with a much more modern look and feel, as well as additional features.
1337x has already been hunted. It has been taken off of Google search queries due to a request (on grounds of copyright, of course) placed by Feel Good Entertainment. Even still, many music torrent lovers are already turning to 1337x as the best backup site in case of The Pirate Bay’s potential demise. In fact, sometimes 1337x is even better than The Pirate Bay, at least in my opinion, in terms of having download ready files that I happen to be looking for.
So, 1337x, it would appear – in addition to a longstanding history as a reputable music torrent site – has a very bright future ahead of it.
How to unblock 1337x
Below we’ll list some of the best proxies we’ve been able to find for you. Some call them mirrors; others call them alternative URLs. In the end though, these are just alternative domain names that let you access everything that the main 1337x domain offers.
Proxy | Rating | Status |
Interface
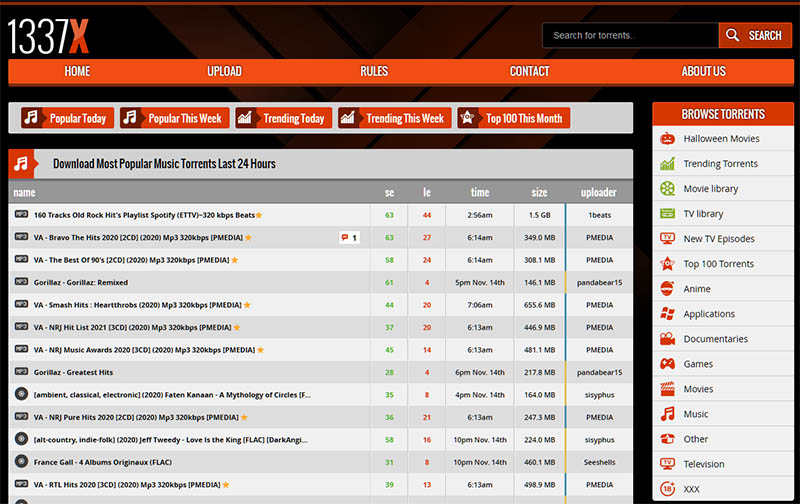
Speaking of 1337x’s redesign circa 2016, I rather like the newer look of the site. It is sleek, clean, minimalist, and easy to use. I tend to enjoy torrent sites that go for a more basic, less cluttered feel, and 1337x may have mastered this. When you first arrive on the site’s home page, you will be greeted by a very modern looking template: a sort of matte black background with a faded red “X” provide the backdrop to a search bar and a line of icons that allow you to browse the site by media type.
Here, you can quickly jump to Music if you just want to browse and discover some new tunes. Otherwise, you can pick from music, TV, Movies, Games, Applications, Anime, Documentaries, Other, and XXX (don’t worry … your secret is safe with me).
Content
From there, the site is very easy to use. It offers up a pretty standard layout for a torrent website. Say, for instance, you typed, I don’t know, A Tribe Called Quest into the search bar. What you’d get in response, on the following page, is every torrent file related to A Tribe Called Quest that 1337x has to offer, from best seed:leech ratio to worst. Pretty typical stuff.
You can also browse torrents by what’s trending today, what’s trending this week, what’s popular today, what’s popular this week, and the top 100 torrents of the month (within a given genre), which makes finding new music much easier than it is on some other music torrent sites.
The thing that I do not like about this site, however, in terms of functionality is the fact that you cannot click a magnet link without clicking into the page of the torrent file. This just makes for necessary extra steps if you find the album that you are looking for, see that it is from a trusted source, and see that it has a decent seeder to leecher ratio.
1337x in numbers
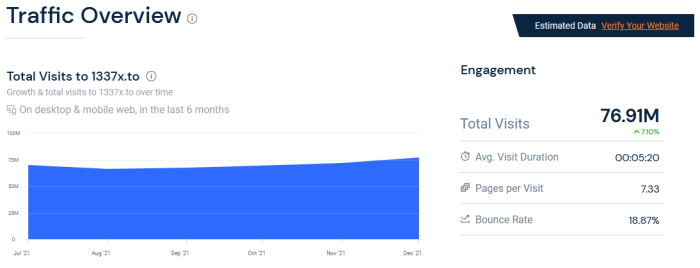
1337x is a big and one of the oldest torrent site. It draws around 70 million users each month. It’s astonishing how this torrent search engine manages to attract tens of millions users. On average, each session on this site lasts for 5 minutes with an average page/visit of 7.40. In addition to that, 1337x has a mind-boggling bounce rate of just 19.30%. That’s the best I’ve seen so far among all the torrent-related sites.
Suggestions that I have for 1337x
Which leads me to the things that I would like to see 1337x do in the future. In addition to adding a magnet link button onto the table of torrent search results, I would also like to see the design slightly tweaked. Instead of clicking into a file type and then having to click into the browsing method of choice, it would be nice if 1337x provided a dropdown menu when you hover your cursor over, say, Music, allowing you to quickly jump to Trending or Top 100 of the month.
Conclusion
1337x is one of the best sources to get the latest games, movies, TV shows, music and apps for free. Simple user interface and a large number of torrents that have been verified by moderators.
PROS
- Lots of great torrent files
- Usually lots of seeders
- Active community of users in comments
CONS
- No magnet link button in search results
- Annoying pop-ups