
Torrenting is a simple means to share massive records data utilizing peer-to-peer (P2P) file-sharing know-how as you’re not depending on a single supply or web site. To obtain records data utilizing torrents, you want a torrent search engine or web site and a torrent client.
There are a lot of torrent websites that you should utilize to obtain the file of your alternative, however selecting the perfect out of them is a process.
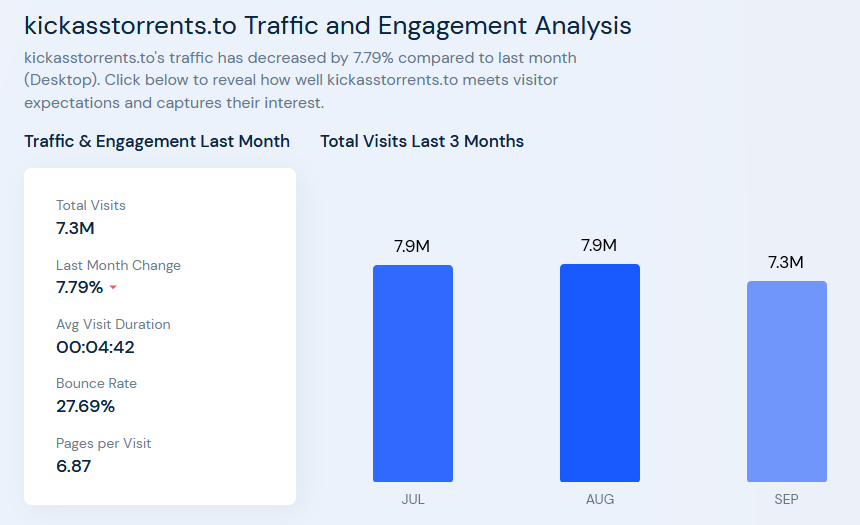
Frequent torrent customers know that Kickass Torrents is without doubt one of the hottest web sites to obtain torrents. That’s the explanation many Kickass proxy websites pop-up on the internet after the well-known torrent portal disappeared.
Is KAT blocked? Can’t access Kickass? Are you looking for the best and most functional Kickass proxy / mirror sites? If you answer yes to any of these questions, you are in the right place today. I will explain step by step how to unlock Kickass without using software, tools or scripts. As we know, Kickass is one of the best sources to download the latest games, movies, TV shows, music and software absolutely free. The simple user interface and the number of torrents make it one of the most popular sites for downloading movies. Instead of using some of the latest streaming video applications, you can simply use them. The site has recently been banned for copyright infringement in many countries, such as the United States, Britain and Canada.
KickAss Proxy Websites Checklist 2023
Right here’s a listing of KickAss torrents proxy websites. We’ve got examined all these Kat proxy websites, and all of the enlisted websites have been working on the time of writing.
New Mirror & Proxy May List 2023
Why Use KickAss Proxy Websites?
There isn’t any means to get KickAss unblocked, however there are proxy websites obtainable that host torrent records data.
If you wish to obtain torrents, you should utilize KickAss proxy websites that supply numerous torrent records data and magnet hyperlinks for downloading your favourite content material
Disclaimer: The torrent websites talked about forward are only for an informational function. We don’t help utilizing them to obtain copyright-protected content material.
How to Access KickassTorrents Through Tor
Tor is free anonymous communication software. It is based on a global network of nodes that routes Internet traffic from one node to another in order to hide the location and use of the user from people performing network monitoring or traffic analysis.
Tor also allows users to access anonymous hidden services that can only be accessed through the Tor network. Such services can be recognized by their suffix .onion domain, which applies only to the Tor network and is not in the root directory of the Internet DNS.
To access the Kickass Tor address, you must first download the Tor browser, which allows you to use Tor on Microsoft Windows, Apple MacOS, or GNU / Linux from here.
1. Tor browser installation is not required. You can simply unzip the downloaded file to any folder and run it by clicking on the application icon.
2. After starting, enter the address kickasto4kpnn.onion in the address bar and press Enter.
3. Sometimes Tor Browser takes time to establish a strong connection. Therefore, downloading the Tor version of KickassTorrents may take several minutes.
Unblock Kickass Torrents through VPN
VPN means a virtual private network that allows you to easily access blocked websites. I used a VPN multiple times to access blocked sites and services, and sometimes multiple sites are blocked due to internal propaganda.
Let us show you how you can use a VPN to unblock the extras of a Chrome or Mozilla browser.
Step 1: Download any VPN in Chrome or Mozilla browser.
I use Betternet for Chrome and you can download Betternet for Windows and Mac OS X.
Step 2: Now click on the three-dot setting in the upper right corner, and then you need to select “additional tools”, and then click “Extensions”.
Step 3: The extensions tab will open and you can enable it. But if you haven’t downloaded it yet, you can download it from Chrome store.
Step 4: You can enable it in incognito mode as well as use it privately.
Step 5: You need to click Betternet or the chosen VPN to enable the service as it is not automatically resolved.
Step 6: Now copy any URL below, paste it into your browser and enjoy it.
Remember that when the VPN server is busy, the download speed will be slow.
Kickass Torrents Alternative Torrent Sites
Even in countries where such sites are banned, there are many alternatives to access kat.to. One of the best ways is to use third-party VPN servers and proxies on the Internet. If you then go online, you definitely need a secure connection to use torrents. Even if Internet service providers or the government prohibit torrent sites, we are here to help you access them directly from your PC. Due to some problems and problems with accessing the server, you may have problems accessing the KAT website. This does not mean that the site or torrent has been blocked.
After its success that lasted more than 12 years, the problems appeared. They announced the closure of kickass.to and from there other pages with the same name and different domains began to appear. They appeared and disappeared: kickasstorrents.unblockninja.com
If the above talked about KickAss torrents proxy websites don’t work, there are a lot of alternate options obtainable. We’ve got ready an in depth article on Kickass Alternatives in 2019 for individuals who are going through issue in accessing the favored torrent search engine.
In our article, you’ll discover many fashionable KickAss search engine alternate options like 1337x, Torrentz2, LimeTorrents, The Pirate Bay and Zooqle for downloading quite a lot of torrents.
There are many referees out there who help us get to the Kickass.to site where the long journeys can be dispensed with for their favorite web delegates they love. If you feel like Kickass unlocking is not available, try something similar to Kickass.to for intermediate research results.
Everyone should work with downloading free materials from the Internet. It is not entirely realistic if someone downloads illegal and morally wrong materials and magazines from the Internet, however, there are many free things open on the Internet that can be downloaded without withdrawal through certain common areas such as the 1377x reseller. However, due to the simplicity of some of the adult content and disturbing content present in the Kickass unlock, this proved to be difficult to get to.
There are not many different ways to get there. One of the standard methods used is the ability to create intermediaries on the site. People at the Kickass Center are open all over the internet, which uses an undefined Kickass partner quick chart database to provide access to most of the site’s page.
Additionally, Kickass torrents (KAT cr) is without doubt one of the best torrents sites after Pirates Bay. The favored BitTorrent website was based in 2008 and tasted its justifiable share of success till it was blocked in 2016.
Nevertheless, like different torrent websites, the Kickass Kat web site has been pulled offline in lots of nations due to the copyrighted content material obtainable on it. After the unique web site was banned, many Kickass torrent mirror websites appeared to entice customers. Even the staffers of the unique Kickass torrent website tried to revive the web site with a brand new kickass website named Katcr.co/full however the website failed to realise a lot traction.
If I am missing something, please let me know your comments in the comment section below. Share this article with your friends so they can take advantage of this helpful guide.
And don’t forget to bookmark this page. We will update this article from time to time with the latest Kickass proxies and alternatives. Thanks.
Conclusion
It’s little question that KickAss Torrent made a well-liked title within the BitTorrent ecosystem. Though, most of it was due to the large quantity of pirated content material it hosted. Anyway, the followers of the defunct website can now solely depend on these Kickass proxy portals. Except they may wish to leap the ship.
PROS
- Wide array of different content
- Tons of seeders, fast downloads
- Verified torrents
- Mobile friendly
CONS
- Annoying ads
- Interruptions in work
- Not original 2016 project













Greate pieces. Keep writing such kind of info on your
page. Im really impressed by your blog.
Hi there, You’ve performed a great job. I’ll certainly
digg it and for my part suggest to my friends. I’m sure they’ll be benefited from this
website.
In fact no matter if someone doesn’t be aware of afterward its up to other users
that they will help, so here it occurs.
helpfull links.
thanks.