The ExtraTorrent Proxy sites are the clones of the Extratorrent.cc website. They have the same layout, torrents, and functionality, just in a different domain. Extratorrent.cc proxy and mirror sites are hosted in countries where ExtraTorrent have not yet been blocked. So if you can’t access the Extratorrent.cc website, you can use this proxy to unblock it.
ExtraTorrent Verified Proxy List 2023
Proxy | Rating | Status |
Extratorrent proxy site allows you to bypass blocks setup by your Internet provider
What is ExtraTorrents proxy?
An Extratorrent proxy is essentially a site that allows you to access ET through the back door. They will make your browser look like it’s in a location where ET is not illegal by masking your IP address and allowing you to access the site.
Sounds simple, right? These sites come and go because they are poorly viewed. In most cases, these sites are also frowned upon, which is why they come and go.
How to unblock ExtraTorrents
If the working Extratorrents web site is blocked in your area, you should use proxies to bypass Extratorrent and obtain torrents. Right here, we’ve listed above some ExtraTorrent proxy websites which you can go to.
If you’re unsure how proxies work, the proxies talked about in our Extratorrent proxy checklist act as intermediate servers that conceal your IP deal with with the intention to entry the web site with out permitting the vacation spot web site to trace you.
Interface
Extra Torrent still has the same iconic layout and design that it had when it originally reigned over the torrenting kingdom. Users of this site can expect a white and blue theme that is crisp, clean, organized, and easy to navigate.
Home page – Extra Torrent offers up a great deal of information and text on its home page. But not in a way that is too overwhelming or cluttered. This is due to the fact that everything on the page is clearly separated and organized. Once you learn the format, it becomes second nature quickly.
In the center, you’ll find a list of the site’s most popular torrents, separated by category. They appear in an index, just like just about every other torrent tracker out there. To the left of this index, though, you will find a collection of the site’s latest articles, most searched torrents, and news (not that this is updated ever). The news section, too, I should note, appears to be now defunct.
Towards the top of the page, you will also find a site menu bar. Here, you can browse Extra Torrent by clicking on any of the following options: Browse Torrents, Search Cloud, Site Stats, Community, and FAQ.
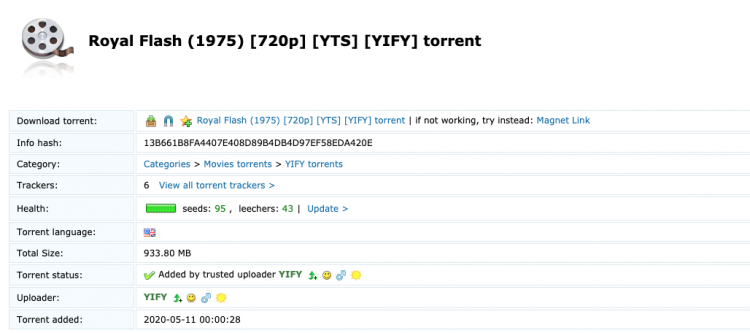
Inner pages – The torrent info and download pages are pretty par for the course as far as torrent trackers are concerned in general. In fact, if you have spent any time on The Pirate Bay, then the format will be familiar. Find all of the torrent info in a chart at the top of the page, description about halfway down (along with any accompanying media if the user included it, such as screenshots and the like), and a comments section at the very bottom. It gets the job done, even if perhaps there are more interactive ways to do it.
Mobile and desktop experience
When it comes to mobile-friendly torrent followers, you can probably find much better ones than Extra Torrent. However, you can definitely find worse things as well. The site is not completely mobile friendly, but it loads and can still be used. It gets much closer to reading filenames and all that.
On the other hand, it’s not as ad-laden as other torrent followers, so it’s a bonus.
Content and Features
As is often the case with clone sites such as this one, you cannot really expect a whole lot in the way of currently active features. What this site is going to be best for is simply to be used as a means of downloading tons of torrents. It is little more than an index, in other words, and many of the original Extra Torrent features are no longer applicable. That being said, it is one of the largest torrent indexes in the world.
A great deal of the items in the site menu bar, for instance, simply bring you back to the site’s home page. Clicking “Forum,” for example, does this. As does trying to view articles, search cloud, and FAQ. The Browse Torrents section, though, still works, offering up a handy way to browse the site’s massive collection of files by category.
Change the DNS server to unblock Extratorrent
ISPs can use DNS blocking, IP address blocking, URL blocking, or some other technical method (if rights holders are happy with it) to block access to torrent websites. DNS level blocks are extremely easy to bypass. You can do it in a hurry.
One of the easiest ways to avoid blocking a website at the DNS level is to use Google’s public DNS. All you have to do is go to your network settings and change your DNS server address to Google’s public DNS address.
On Windows 10 PC:
Go to Control Panel> Network and Internet> Network and Sharing Center. In the left panel, click Change adapter settings
Right click on the connection type (possibly Ethernet or Wi-Fi) of your choice and go to Properties
Scroll down the list of items to find Internet Protocol Version 4 (TCP / IPv4). Click it once to select it, then click Properties.
At the bottom of the box is “Use the following DNS server addresses.” Select this option and enter 8.8.8.8 and / or 8.8.4.4
Popular public DNS servers
Google DNS: 8.8.8.8 | 8.8.4.4
Cloudflare: 1.1.1.1 | 1.0.0.1
OpenDNS: 208.67.222.222 | 208.67.220.220
Comodo: 8.26.56.26 | 8.20.247.20
Quad9 DNS: 9.9.9.9 | 149.112.112.112
Adguard DNS: 94.140.14.14 | 94.140.15.15
Click OK and you’re done.
The process is very similar on Windows 7/8 / 8.1 and even on Mac computers. Just find the network settings and change the DNS server address.
We don’t know what type of blocking method other ISPs will use, but the options below should be enough to bypass a number of site blocking techniques.
How does ExtraTorrent Torrent work?
ExtraTorrent Torrent has its own website and hosting services. Thus, the downloaded files have the correct security and access links. ExtraTorrent downloads various files to its servers and storage, creating links and trackers for downloading torrent files directly to your device. When a person uploads a file, he can install or share it using the ExtraTorrent torrent tracker. This is a very simple process.
All you have to do is insert the file into the torrent download software, such as Azure, μTorrent or BitTorrent, and download it to your computer. Then save the file in the same place and do not delete the torrent file from the μTorrent or BitTorrent software. Allow μTorrent software to install and compare content. This option is activated by default. This way you can share content with many people, and they can also share content with you through ExraTorrent Torrent. This is how ExraTorrent Torrent works.
Beware of scammers!
Special care required! There are a number of fake websites that are trying to attract users in order to increase their traffic and make money from it. He often uses the so-called “Extratorrent Mirror”, a mirroring of the previously official domains of Extratorrent.cc website. These pages look exactly the same as the correct page and many users don’t even notice that you are on the wrong website. Do not try to download any binary client, exe file e.t.c.
Conclusion
Resurrection – It has taken quite a bit of time, but it appears as if a true working clone of Extra Torrent has finally surfaced, in the form of Extratorrent.unblockninja.com. Not only does this site have everything that Extra Torrent ever had on it, but it also is constantly growing and allowing new members to register. Extra Torrent has risen from the grave, it seems, and is picking up right where it left off.
PROS
- Massive collection of torrents
- Tons of seeders
- Easy torrent browsing
- Community features no longer work
CONS
- Lots of missing features (clone site)